Welcome to today's threat briefing for 25 March 2026. As a senior penetration tester actively engaged in defending Australian networks, I am observing an unprecedented level of volatility in our local threat landscape. Over the last 24 hours, adversary behaviour has demonstrated a rapid shift towards exploiting misconfigured cloud environments, weaponising artificial intelligence, and aggressively targeting critical supply chains.
Australian Daily Cyber Threat Briefing: AI Exploits, API Abuse, and Evolving Ransomware
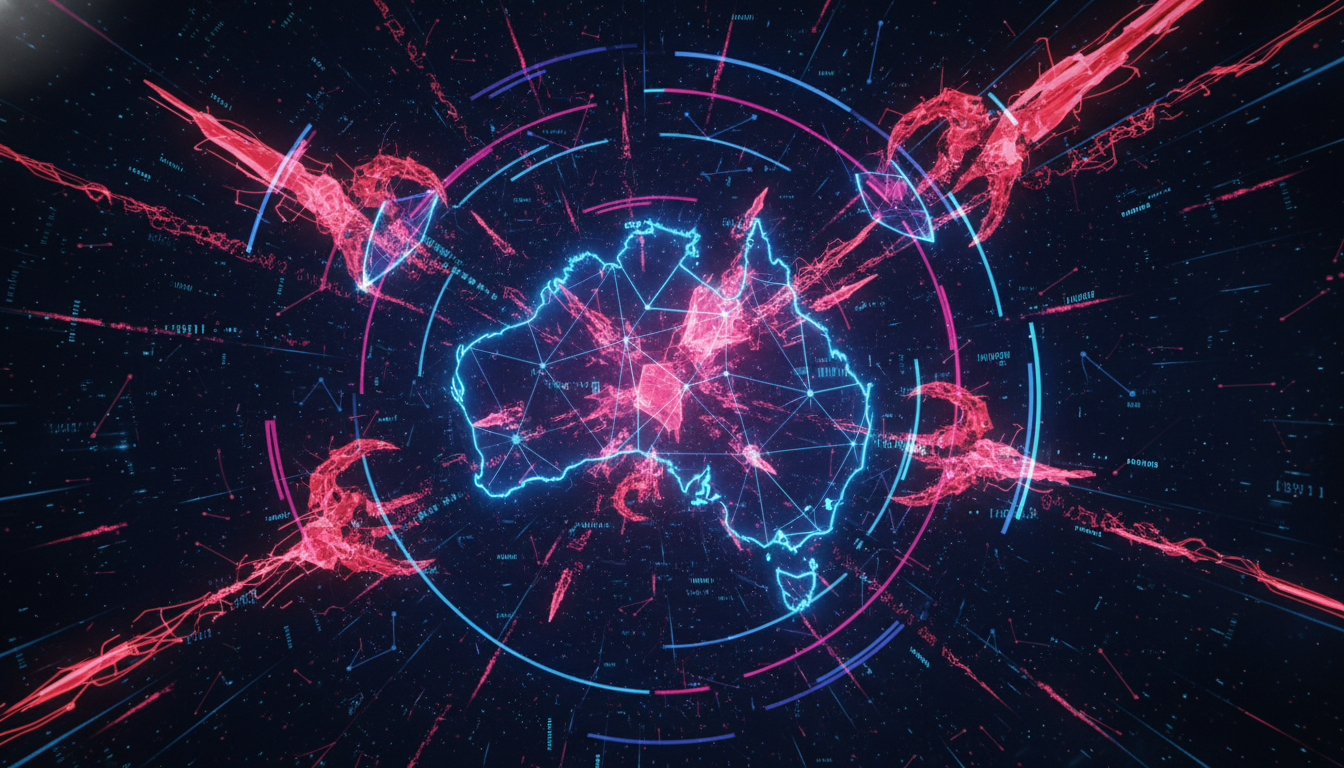
As a senior penetration tester, I continually analyse the tactics, techniques, and procedures (TTPs) deployed against Australian organisations. Over the last 24 hours, our threat intelligence and incident response telemetry have highlighted a highly volatile landscape. We are witnessing aggressive automated exploitation of cloud environments, rampant API abuse, and novel attacks against integrated AI systems. The 2026 Armis Cyberwarfare Report recently noted that Australia is experiencing a surging volume of cyberwarfare attacks, underscoring the urgent need for a proactive, "assume breach" mentality.
Australian Cyber Threat Landscape: Daily Briefing
As a senior penetration tester analysing adversary behaviour on the frontlines, I am observing an unprecedented level of volatility in the Australian cyber threat landscape. The window between vulnerability disclosure and active exploitation has collapsed to mere days, if not hours. Over the last 24 hours, threat actors have escalated their weaponisation of artificial intelligence, heavily exploited cloud misconfigurations, and capitalised on critical zero-day vulnerabilities across multiple key industries.
Daily Cyber Threat Briefing: Ransomware, Cloud Exploits, and AI-Driven Attacks in Australia
As a senior penetration tester actively analysing adversary behaviour and responding to frontline incidents, I am tracking a highly volatile threat landscape across Australia. Over the past 24 hours, our telemetry and threat intelligence indicate that the window between vulnerability disclosure and active exploitation has collapsed to mere days. Threat actors are rapidly weaponising artificial intelligence, exploiting cloud misconfigurations, and capitalising on critical web application and API vulnerabilities.
Daily Threat Briefing: Australian Cyber Landscape Deep Dive
As a senior penetration tester actively analysing adversary behaviour and responding to frontline incidents, I am tracking a highly volatile threat landscape across Australia. Over the past 24 hours leading up to 20 March 2026, our telemetry and incident response engagements reveal a collapse in the window between vulnerability disclosure and active exploitation. Threat actors are aggressively weaponising artificial intelligence, exploiting misconfigured cloud environments, and capitalising on critical web application and API vulnerabilities.
Daily Cyber Threat Briefing – Australia: AI Weaponisation, Cloud API Exploits, and Sector Sieges
As a senior penetration tester actively analysing adversary behaviour and frontline incident telemetry, I am tracking a highly volatile threat landscape across Australia. The newly released 2026 Armis Cyberwarfare Report (published today, 19 March 2026) highlights a sharp 72% rise in nation-state activity targeting Australian entities over the last year. Concurrently, the window between vulnerability disclosure and active exploitation has collapsed to mere days. Adversaries are aggressively exploiting misconfigured cloud environments, weaponising generative AI, and capitalising on critical API vulnerabilities to bypass traditional perimeter defences.
Daily Threat Briefing: Australian Cyber Landscape & Emerging Vulnerabilities
As of 18 March 2026, the Australian cyber threat landscape continues to escalate, marked by highly destructive attacks, aggressive exploitation of zero-day vulnerabilities, and the rapid weaponisation of AI by sophisticated threat actors. With the Federal Court recently imposing a landmark AUD 2.5 million penalty against an Australian financial services firm for cybersecurity governance failures, organisations across the nation are under immense regulatory and operational pressure to mature their cyber defences.
Australian Cyber Threat Briefing: Surging Ransomware, AI Exploits, and Critical API Vulnerabilities
As of 17 March 2026, the Australian cyber threat landscape is escalating at an unprecedented pace, driven by highly sophisticated threat actors exploiting novel vulnerabilities across cloud, AI, and API environments. As a senior penetration tester, I spend my days simulating these exact adversary behaviours to uncover weaknesses before they are weaponised. Over the last 24 hours, we have observed a significant uptick in targeted attacks against critical Australian sectors, compounded by the rapid exploitation of newly disclosed Common Vulnerabilities and Exposures (CVEs).
Daily Australian Cyber Threat Briefing: Escalating AI Exploits, Ransomware, and Cloud Breaches
As a senior penetration tester actively analysing adversary behaviour and responding to frontline incidents, I am tracking an exceptionally volatile threat landscape across Australia today, 16 March 2026. Over the past 24 hours, the window between vulnerability disclosure and active exploitation has collapsed from weeks to mere hours. We are observing threat actors aggressively weaponising artificial intelligence, exploiting cloud misconfigurations, and capitalising on critical zero-day vulnerabilities to bypass traditional perimeter defences. With Australia’s mandatory ransomware reporting laws in full enforcement and the new Cyber Security (Security Standards for Smart Devices) Rules 2025 officially active this month, the stakes for Australian organisations have never been higher.
Australian Daily Threat Briefing: AI Exploits, Ransomware Resurgence, and Zero-Day Fallout
As a senior penetration tester actively analysing adversary behaviour and responding to frontline incidents, I am tracking a highly volatile threat landscape across Australia today. Over the past 24 hours, the window between vulnerability disclosure and active exploitation has collapsed to mere days. We are seeing threat actors rapidly weaponising artificial intelligence, exploiting cloud misconfigurations, and capitalising on critical zero-day vulnerabilities.