Beyond the Checkbox: Why Continuous Penetration Testing & Red Teaming Are Essential in 2026
The cybersecurity landscape has reached a pivotal turning point in 2026. We are no longer living in an era where cyber threats evolve month by month; today, they evolve minute by minute. With the explosive rise of AI-assisted exploit chaining, sophisticated Phishing-as-a-Service (PHaaS), and automated vulnerability discovery, threat actors are moving at machine speed.
If your organisation relies solely on a traditional, once-a-year pen test to check a compliance box, you are inherently operating with a massive blind spot. By the time that static PDF report lands on your desk, your digital environment has already shifted, and new security weaknesses have likely emerged. In Australia, regulatory bodies and enterprise boards are waking up to this reality, sparking a massive shift toward continuous, intelligence-led offensive security.
Whether you are seeking a premier penetration testing service or looking to test your in-house defenders through a full-scale red team engagement, understanding how testing methodologies have evolved is crucial for protecting your bottom line. Let’s dive into the current state of penetration testing Australia and how you can stay ahead of the curve.
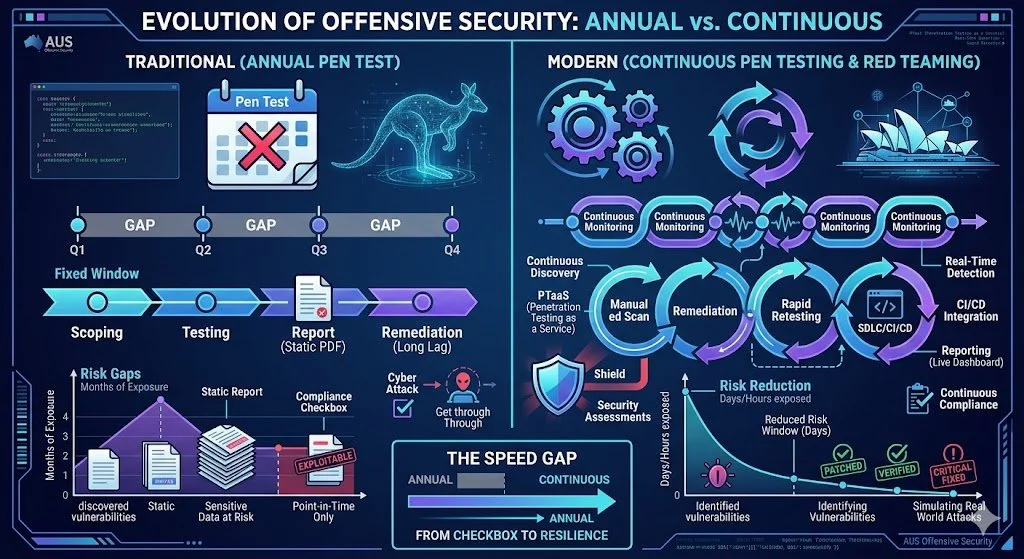
Evolution of offensive security: Annual vs Continuous
Why Annual Penetration Testing is Failing Modern Businesses
In the past, organisations scheduled a penetration test service once a year to satisfy auditors and renew their cyber insurance. While point-in-time assessments still hold value for specific baseline checks, they fail to account for the velocity of modern development. Every time your engineering team pushes a code update, launches a new microservice, or modifies a cloud configuration, your attack surface changes.
The "Speed Gap" and AI-Assisted Attacks
In 2026, attackers are heavily leveraging generative AI to automate reconnaissance and craft highly convincing, hyper-personalised lures. They chain together low-severity vulnerabilities to execute a devastating cyber attack. This creates a "speed gap" between rapid threat evolution and static, calendar-based testing cycles. If an exploitable flaw is introduced to your network in February, waiting until your annual test in November leaves your sensitive data exposed for nine months. A modern cyber security posture demands agility.
Evolving Australian Regulatory Pressures
The Australian regulatory environment is actively tightening to combat these threats. With the expansion of the Security of Critical Infrastructure (SOCI) Act, APRA CPS 234, and strict PCI DSS 4.0 enforcement, regulators no longer accept simple policy documentation. They require demonstrable technical validation of your security controls. Boards now expect quantified risk reduction, pushing organisations to partner with an elite penetration testing provider that can translate technical risks into business impact.
The Rise of Penetration Testing as a Service (PTaaS)
To bridge the speed gap, the industry is heavily adopting penetration testing as a service (PTaaS). This model represents a fundamental shift in how testing services are delivered.
Instead of a siloed engagement, a penetration test as a service integrates directly into your Software Development Life Cycle (SDLC) and CI/CD pipelines. This approach combines the scale of automated vulnerability scanning with the contextual intelligence of an expert human penetration tester.
When you engage reputable penetration testing service providers for PTaaS, you receive:
Continuous Monitoring: Rapid identification of new exposures in real-time.
On-Demand Retesting: The ability to instantly verify that a vulnerability has been successfully remediated by your development team.
Actionable Dashboards: Live insights into your risk posture rather than a static annual report.
By moving to continuous penetration testing services, Australian businesses reduce their window of exposure from months to mere days, ensuring exploitable vulnerabilities are patched before threat actors can weaponise them.
Red Teaming: Simulating Real World Attacks
While standard penetration test services focus on finding as many vulnerabilities as possible within a defined scope, red teaming takes a vastly different approach. Red teaming is about simulating real world attacks to test how well your people, processes, and technology respond to a determined, covert adversary.
A mature penetration testing service in australia will deploy a red team to mimic the exact Tactics, Techniques, and Procedures (TTPs) of known threat actors targeting your specific industry. This multi-layered assessment often occurs over weeks or months and tests the defensive capabilities (the "Blue Team") of your organisations.
Red teaming pushes beyond digital borders, often incorporating:
Advanced Social Engineering: Spear-phishing executives, voice cloning (vishing), and deepfake exploitation to bypass initial access controls.
Physical Breaches: Assessing facility security by attempting to clone badges, tailgate employees, or plant rogue devices on the corporate network.
Evasion Tactics: Testing if the Security Operations Centre (SOC) can detect lateral movement, privilege escalation, and data exfiltration without alerting the attackers.
For organisations with a mature security posture, red teaming provides the ultimate reality check.
Core Focus Areas for 2026: APIs, Cloud, and Identity
As perimeters dissolve and workforces remain distributed, threat actors have shifted their crosshairs. A comprehensive security strategy must prioritise the following critical areas:
1. API Penetration Testing Services
Application Programming Interfaces (APIs) are the backbone of modern digital architecture, connecting countless microservices and third-party apps. Unfortunately, they are also frequently under-tested and over-trusted. In 2026, APIs are essentially the backdoor to your data. Specialized API penetration testing services are crucial to identify broken object level authorisation (BOLA), mass assignment flaws, and rate-limiting failures that automated scanners completely miss.
2. Active Directory Penetration Testing Service
If a threat actor gains a foothold in your network, their next immediate goal is lateral movement and privilege escalation. Your Active Directory (AD) or Entra ID environment is the keys to the kingdom. An expert active directory penetration testing service uncovers misconfigurations, weak password policies, and excessive permissions that could allow an attacker to achieve total domain compromise.
3. Application Security
Your customer-facing applications are your most visible attack surface. Engaging dedicated web application testing and a robust mobile application penetration testing service ensures that your software is resilient against complex logic flaws, session hijacking, and insecure data storage. For organisations heavily invested in mobile ecosystems, engaging recurring mobile application penetration testing services is non-negotiable to protect consumer trust and comply with global privacy laws.
How Penetration Testing Involves Identifying Vulnerabilities
If you are new to the process, you might wonder what a thorough engagement looks like. Penetration testing involves a highly structured methodology to ensure safety, comprehensiveness, and accuracy.
Scoping and Rules of Engagement: The provider works collaboratively with you to define what systems are in bounds, what techniques are off-limits, and the ultimate goals of the assessment.
Reconnaissance & Threat Modelling: Testers gather open-source intelligence (OSINT) to understand your digital footprint, identifying exposed credentials or shadow IT assets.
Identifying Vulnerabilities: Using a blend of bespoke automated tooling and deep manual analysis, experts search for weak points.
Exploitation: The critical step. Testers actively exploit the findings to validate the risk. This proves whether a theoretical vulnerability can actually lead to unauthorised access.
Reporting and Remediation: You receive a prioritised, highly detailed report outlining the business impact of each flaw, alongside precise, actionable remediation guidance.
Understanding Penetration Testing Cost in Australia
Budgeting for security is a common concern. Penetration testing cost varies wildly depending on the size of your infrastructure, the depth of the assessment, and the prestige of the firm. Below is a high-level guide to help you budget for penetration testing sydney and across Australia in 2026.
| Service Type | Typical Scope | Estimated Cost (AUD) |
|---|---|---|
| Web / Mobile App Test | Single application, API endpoints, role-based access checks. | $8,000 - $25,000+ |
| Internal Network Test | Active Directory, workstations, internal servers, lateral movement. | $12,000 - $35,000+ |
| Cloud Infrastructure Test | AWS/Azure/GCP configurations, IAM roles, container security. | $15,000 - $40,000+ |
| Full Red Team Engagement | Multi-month simulation, physical security, social engineering, evasion. | $45,000 - $150,000+ |
| Continuous PTaaS | Ongoing SDLC integration, automated scanning, manual verification. | $3,000 - $10,000+ / month |
Note: These estimates are indicative. Always request a custom scoping call with your provider to get an accurate quote tailored to your environment.
Types of Penetration Tests You Should Consider
Depending on your maturity and specific security standards, there are several types of penetration tests to integrate into your strategy:
Black Box Testing: Testers are given zero prior knowledge of the environment, perfectly mimicking an external, unauthenticated attacker.
Grey Box Testing: Testers are provided with basic user credentials and partial knowledge. This is the most common and efficient approach for application penetration testing, simulating a malicious insider or a compromised user account.
White Box Testing: Testers have full access to source code and architecture diagrams. This provides the most comprehensive evaluation of your code base and underlying logic.
Securing Your Future Today
The question is no longer if your organisation will be targeted, but when, and whether your defences will hold up against an adversary operating at the speed of modern AI. Clinging to outdated, annual compliance-driven testing methodologies is a dangerous gamble with your company's reputation and intellectual property.
By embracing continuous testing models, robust API and cloud scrutiny, and realistic red teaming exercises, you transition your security posture from reactive to proactively resilient.
Ready to mature your security operations and close the speed gap? Contact our expert team today for a confidential scoping call and customised quote. Let’s collaborate to build a defence strategy that stands up to the reality of 2026.